Effective vulnerability management teams require contextual awareness to make informed, intelligent remediation decisions. So why don’t prevailing security tools provide real context?
There are products that can tell you what vulnerabilities exist in your network. Our platform goes beyond that by making sense of the mountain of data, allowing you to analyze and prioritize risk in minutes not days.
Effective vulnerability management teams require contextual awareness to make informed, intelligent remediation decisions. So why don’t prevailing security tools provide real context?
There are products that can tell you what vulnerabilities exist in your network. Our platform goes beyond by providing real contextual awareness to help you analyze and prioritize risk in minutes not days.
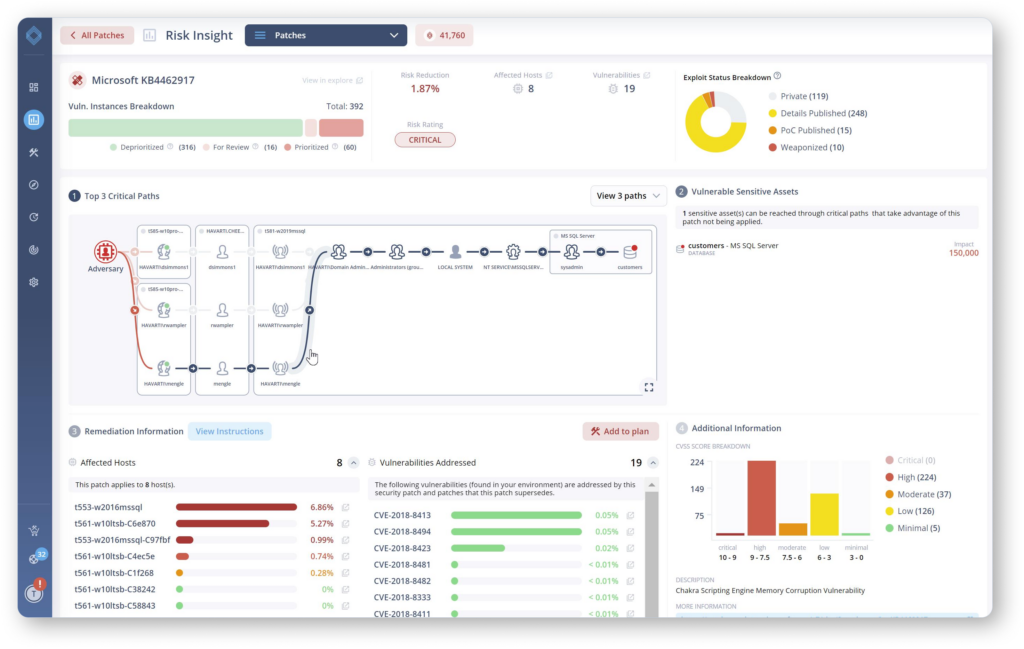
Blast Radius Insights

“If this account is compromised, where would the attacker go next?”
No asset or user account is an island. Connect the dots between CVEs, access rights, and your most sensitive assets.
Thousands of assets may be affected by a CVE, but not all assets are created equal. Quickly determine the downstream impact of an exploit in a specific part of your environment.
Clearly demonstrate to stakeholders and system owners how their choices are presenting risk to the organization as a whole.
Vulnerability Prioritization

“A patch is needed on 1000 machines, but which one is best to start with?“
Meanwhile, only a tiny fraction of vulnerabilities in your environment are practically exploitable given the controls you have in place.
When it comes to urgent fixes, focus your team on those devices present demonstrable security risk.
Strategic Intrusion Detection

“What should I monitor more closely while I wait for that fix to roll out?”
Remediation Planning

“Now that we know what to fix, how do we get it done?”
Automatically break down issues according to system owner
Create actionable tasks with easy to understand instructions
Export tasks as tickets to multiple third-party products
Track status of tasks over time and cross-validate completion
User Access Rights Analysis
 “Where are we exposed to account-related risks, such as credential theft and over-provisioning?”
“Where are we exposed to account-related risks, such as credential theft and over-provisioning?”

“If this account is compromised, where would the attacker go next?”
No asset or user account is an island. Connect the dots between CVEs, access rights, and your most sensitive assets.
Thousands of assets may be affected by a CVE, but not all assets are created equal. Quickly determine the downstream impact of an exploit in a specific part of your environment.
Clearly demonstrate to stakeholders and system owners how their choices are presenting risk to the organization as a whole.

“A patch is needed on 1000 machines, but which one is best to start with?“
Meanwhile, only a tiny fraction of vulnerabilities in your environment are practically exploitable given the controls you have in place.
When it comes to urgent fixes, focus your team on those devices present demonstrable security risk.

“What should I monitor more closely while I wait for that fix to roll out?”

“Now that we know what to fix, how do we get it done?”
Automatically break down issues according to system owner
Create actionable tasks with easy to understand instructions
Export tasks as tickets to multiple third-party products
Track status of tasks over time and cross-validate completion
 “Where are we exposed to account-related risks, such as credential theft and over-provisioning?”
“Where are we exposed to account-related risks, such as credential theft and over-provisioning?”
See how DeepSurface provides experienced security professionals with the tools they need to: