TL;DR
Older versions of Adobe Acrobat Reader are vulnerable to local privilege escalation (LPE) attacks under certain conditions on Windows platforms. This would allow an attacker to perform a local privilege escalation attack against Acrobat Reader users using the same Windows system. Through our responsible disclosure program Adobe was contacted and provided a fix for this issue. Adobe also issued CVE-2021-35982 to track the vulnerability.
Overview
Adobe Acrobat Reader is a popular application for viewing and interacting with PDF documents.
As part of our security research, we find that many products are installed with insecure file system permissions. In this case, we found that when users install Acrobat Reader on Windows in a location other than the default, it allows any other user on the same system to take control of the accounts of users who use Acrobat Reader. Because of a bug that causes improper configuration of permissions in the installation directory, an attacker can perform DLL hijacking/sideloading attacks.
For more information on this vulnerability class, see our previous blog post on the topic, as well as some of the vulnerabilities we have published previously (CVE-2021-29221, CVE-2021-26556).
Exploitation
To demonstrate this flaw, we downloaded Acrobat Reader (the latest version at that time, being 2021.005.20048) from https://get.adobe.com/reader/enterprise/.

We also changed the installation directory to C:\adobe, which can be created through the installer GUI.
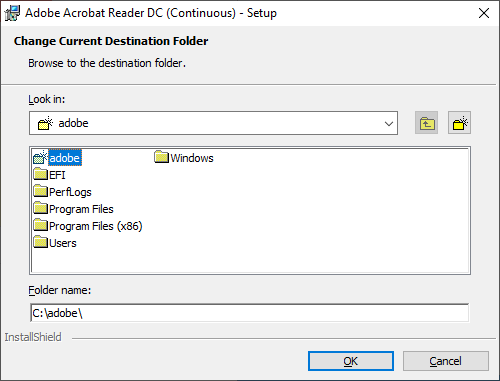
Aside from a custom installation directory, we use the default options.
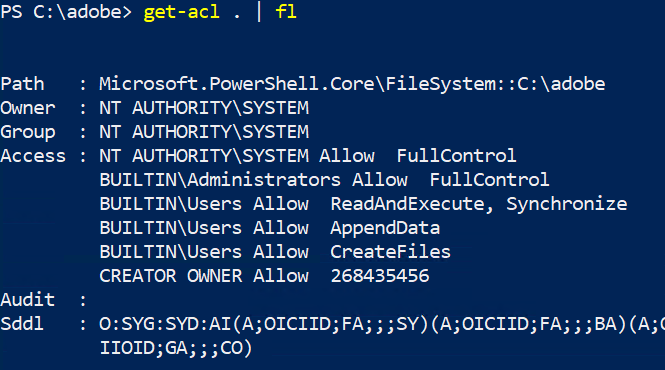
After installation, we found that the installation folder had improper permissions in that it included, BUILTIN\Users Allow *, which was inherited from the drive root. This gives any local user the ability to create new files (but not modify existing files) in the installation directory.
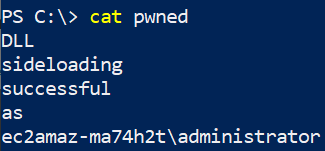
To fully demonstrate the implications of this vulnerability, first create a new unprivileged user. Then, as this user, download the SensApi.dll file available in our GitHub Repository and move it into the C:\adobe\Reader directory. (For more information on how this file was generated, see the README.md file in the same repository.)
Now as the privileged user, start Acrobat Reader. You should see a number of terminal windows appear as the payload gets executed. Assuming the default payload, you should also see a message written to the file C:\pwned.
Timeline
| June 10, 2021 | Submitted to https://hackerone.com/adobe |
| July 2, 2021 | After hearing no response from Adobe, requested an update. |
| July 22, 2021 | Reminded Adobe of DeepSurface Security’s 90-day disclosure policy |
| July 22, 2021 | First response from Adobe indicating engineering team had been working on a fix with an anticipated September release date |
| July 22, 2021 | DeepSurface confirmed this timeline was acceptable. |
| September 14, 2021 | Updated Adobe Reader released along with advisory for CVE-2021-35982. |
The Fix
Adobe released a security bulletin to address this issue. Please see the details in: https://helpx.adobe.com/security/products/acrobat/apsb21-55.html
We recommend users ensure any existing Acrobat Reader installations (particularly those installed outside of C:\Program Files) are examined to ensure filesystem permissions are secure.
Acknowledgements
We would like to thank the Adobe security team for their support and thoroughness in investigating and fixing this issue.
